AI Cybersecurity Platforms: The Intelligent Shield for 2026 and Beyond
Estimated reading time: 8 minutes
Key Takeaways
- AI cybersecurity platforms are integrated systems using machine learning and behavioral analytics for real-time threat detection and prevention, moving beyond traditional signature-based security.
- 77% of organizations are already running generative AI or large language models in their cybersecurity stack, signaling massive adoption.
- Automated threat detection is the core, with 96% of professionals agreeing AI improves speed and efficiency in identifying novel threats.
- Ransomware AI defense is critical as 73% of professionals face AI-powered threats, requiring proactive anomaly detection and automated response.
- Zero Trust AI enables continuous verification and dynamic policy enforcement, making Zero Trust Architecture feasible at scale.
- The security AI 2026 landscape will be defined by platform consolidation, governance challenges, and a shift towards preemptive, predictive defense.
Table of contents
- AI Cybersecurity Platforms: The Intelligent Shield for 2026 and Beyond
- Key Takeaways
- The New Era of Cyber Defense
- Automated Threat Detection: The Beating Heart of AI Security
- Ransomware AI Defense: Countering the Evolved Threat
- Zero Trust AI: The Framework for Continuous Verification
- Security AI 2026: Trends Shaping the Future
- Frequently Asked Questions
As cyber threats escalate in sophistication and scale, the digital battleground of 2026 demands a new class of defender. Enter ai cybersecurity platforms—integrated systems that leverage machine learning and behavioral analytics for real-time threat detection and prevention. This is a fundamental shift from the reactive, signature-based security of the past, which relied on static threat definitions and was often a step behind attackers. For a broader look at this transformation, see our guide on breakthrough AI cyber defense.
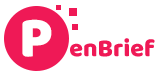
The critical shift is here: Instead of waiting for a known malware signature, these platforms predict and prevent threats by analyzing anomalies in vast data streams. This evolution is driven by sheer necessity, fueled by an explosively expanding attack surface that now includes countless SaaS integrations, IoT devices, and autonomous AI agents. The old walls are crumbling; the new defense is intelligent, adaptive, and always on.
The adoption stats speak volumes: 77% of organizations are already running generative AI or large language models in their cybersecurity stack, and 67% have deployed agentic AI for autonomous or semi-autonomous operations. This isn’t a future trend—it’s the current reality of enterprise security.
This post will satisfy your informational intent by diving deep into the core components that make these platforms revolutionary: automated threat detection, ransomware ai defense, zero trust ai, and the overarching security ai 2026 trends. Together, they form the engine of a modern, resilient defense.
Automated Threat Detection: The Beating Heart of AI Security
At its core, automated threat detection is the defining capability of any true ai cybersecurity platform. It’s where artificial intelligence and machine learning algorithms process immense, heterogeneous datasets—network traffic, user behavior, endpoint telemetry, application logs—in real-time to spot deviations that signal a threat, doing so at a speed and scale impossible for human analysts.
The impact is undeniable. According to recent data, 72% of cybersecurity professionals identify anomaly detection and novel threat identification as delivering the most impact from AI, with automated response following at 48%. Perhaps more tellingly, 96% agree that AI improves the speed and efficiency of their security operations.
Here’s how it works in practice:
- Intelligent Prioritization: AI doesn’t just flood analysts with alerts. It correlates events, assesses risk based on context (e.g., is this a privileged user? Is this a critical server?), and surfaces only the most pressing incidents. This directly combats the crippling alert fatigue that plagues traditional Security Operations Centers (SOCs).
- Unified Visibility: The power is in integration. 93% of security professionals now favor integrated platforms over a patchwork of point products. An AI platform can see across email, network, cloud workloads, and identity systems simultaneously, connecting dots that would otherwise remain invisible in siloed tools.
Think of it like this: Traditional security is a guard at a gate, checking IDs against a static watchlist. Automated threat detection powered by AI is a team of vigilant sentries scanning the entire crowd, noticing the subtle shift in posture, the unusual pattern of movement, the disguised face—the anomalies that reveal malicious intent before an attack even begins.
This constant, intelligent vigilance is precisely what’s needed to counter today’s most aggressive threats, particularly the evolved menace of ransomware.
Ransomware AI Defense: Countering the Evolved Threat
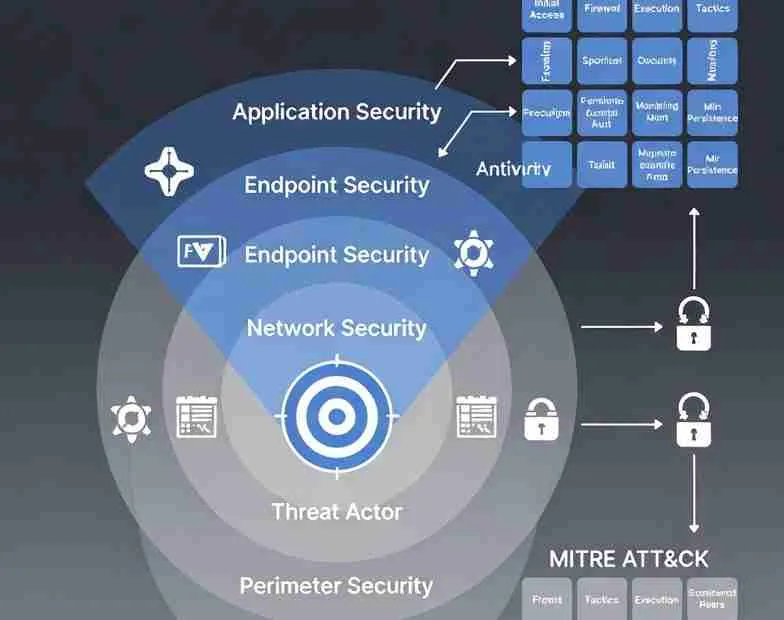
Ransomware has evolved from a blunt instrument to a precision-guided, AI-powered threat. Defending against it requires an equally sophisticated response, making ransomware ai defense a paramount application for modern platforms. The threat is real and present: 73% of security professionals report AI-powered threats hitting their organizations, including hyper-personalized phishing (50%), automated exploit chaining (45%), and adaptive malware (40%). To understand the full scope of this evolving danger, explore our analysis of explosive cybersecurity threats.

Modern ai cybersecurity platforms coordinate a full countermeasure chain:
- Proactive Anomaly Detection: AI monitors for early ransomware indicators—unusual file access patterns, mass file renames, or spikes in encryption-related process calls—often stopping the attack before widespread encryption occurs.
- Automated Isolation & Containment: Upon detection, the platform can automatically segment infected endpoints or network segments, preventing lateral movement and “islanding” the threat.
- Deception Technology: AI can deploy and manage honeypots—decoy files, servers, or network shares that mimic real assets. When ransomware interacts with these traps, it reveals itself immediately, allowing for swift containment.
- Predictive Intelligence: By analyzing global threat feeds and attacker behaviors, AI can predict which vulnerabilities or entry points ransomware gangs are likely to target next, enabling preemptive patching and hardening.
Here’s the technical detail: Modern ransomware often deploys via behavioral deviations, like a user process suddenly attempting to encrypt hundreds of files. AI models, trained on normal behavior baselines, spot this deviation instantly. Coupled with deception, it can lure the ransomware into a controlled honeypot environment, analyzing its behavior without risking real data.

Imagine this scenario: Ransomware creeps into your network via a phishing email. Before it can call home to its command server, AI spots the anomalous network connection. As it begins to encrypt its first few files, the behavioral AI engine triggers. The infected device is automatically isolated from the network, and the attack is halted. Recovery processes, tied to verified clean backups, are initiated—all within minutes, with minimal human intervention.
This level of integrated, automated defense is a strategic priority. 65% of security leaders are prioritizing adding AI-powered tools, with 57% focused on better integrating their existing security stack. This seamless integration naturally dovetails with the most robust security framework available today: Zero Trust, supercharged by AI.
Zero Trust AI: The Framework for Continuous Verification
Zero Trust Architecture (ZTA) operates on a simple, powerful principle: “Never trust, always verify.” But implementing this at scale across dynamic cloud environments and mobile workforces is where traditional approaches stall. This is where zero trust ai becomes the critical enabler, seamlessly integrated within ai cybersecurity platforms to provide the continuous monitoring and dynamic risk assessment ZTA demands.

AI breathes life into Zero Trust by moving it from a static policy framework to an adaptive, intelligent system:
- Micro-Segmentation Enforcement: AI analyzes application dependencies and traffic flows to automatically define and enforce fine-grained network segmentation policies, isolating workloads and containing breaches.
- Risk-Based Authentication: Instead of one-size-fits-all access rules, AI scores each login attempt in real-time. A login from a new geography combined with a request for sensitive data might trigger step-up authentication (like MFA), while a routine access from a known device and location proceeds smoothly.
- Real-Time Policy Adjustment: AI continuously learns from user and device behavior. If a device starts behaving anomalously (e.g., scanning internal ports), its risk score increases, and AI can dynamically restrict its access privileges without waiting for a policy update.
In cloud-native environments, this is especially potent. AI feeds continuous authentication and behavioral data from cloud workloads into its models, auto-learning and adapting protections as the environment scales and changes. For a deep dive into securing these dynamic environments, read our guide on unbeatable AI cloud security.
Technical Note: Traditional ZTA can generate overwhelming amounts of log data and policy exceptions. AI solves this by assigning dynamic risk scores (e.g., 0-100) based on hundreds of contextual factors. A score exceeding a threshold automatically triggers a policy action, like terminating a session or requiring re-authentication.
Think of it not as a single gatehouse but as a fortress where every corridor, every door, has an AI sentry. This sentry doesn’t just check your pass once; it continuously observes your behavior, verifying your identity and intent at every step. This is the power of zero trust ai—making continuous verification not just possible, but practical. As we look ahead, this intelligence becomes the foundation for the next wave of security innovation.
Security AI 2026: Trends Shaping the Future
The trajectory of security ai 2026 is being written now, defined by rapid adoption, emerging challenges, and a fundamental shift in strategy. The trends within ai cybersecurity platforms reveal an industry at an inflection point.

The Governance Gap: While 77% of organizations run generative AI in their security stack, only 37% have formal policies governing its use. Even more striking, only 14% allow AI to take independent remediation actions. This highlights a critical need for ethical AI frameworks, oversight, and human-in-the-loop controls to manage risk and ensure accountability.
Platform Consolidation: The era of tool sprawl is ending. 93% of professionals now prefer platform-based security solutions (up from 87% in 2025), seeking the unified visibility, reduced complexity, and integrated AI analytics that only a cohesive platform can provide.
.png)
The Rise of the Managed AI SOC: Expertise is scarce. 85% of organizations prefer managed Security Operations Centers (SOCs) over building in-house capabilities. This trend points toward AI platforms being increasingly delivered as a service, with experts managing the AI models, tuning detection rules, and guiding response.
<