AI Cybersecurity Platforms: The Unified Shield for 2026 and Beyond
Estimated reading time: 12 minutes
Key Takeaways
- AI cybersecurity platforms are integrated, AI-native solutions essential for countering the machine-speed attacks of 2026.
- Core functions include automated threat detection for real-time anomaly analysis and ransomware AI defense for proactive containment.
- These platforms are the engine for Zero Trust AI, operationalizing “never trust, always verify” at scale.
- The roadmap to Security AI 2026 points toward autonomous, predictive systems that defend against AI-on-AI threats.
- Adopting a unified platform is critical for building resilient, future-proof cyber defenses.
Table of contents
- AI Cybersecurity Platforms: The Unified Shield for 2026 and Beyond
- Key Takeaways
- The Escalating Threat Landscape: Why Old Defenses Fail
- What Is an AI Cybersecurity Platform?
- The Core Engine: Automated Threat Detection
- A Critical Application: Ransomware AI Defense
- The Strategic Framework: Zero Trust AI
- The Future Roadmap: Security AI 2026
- Frequently Asked Questions
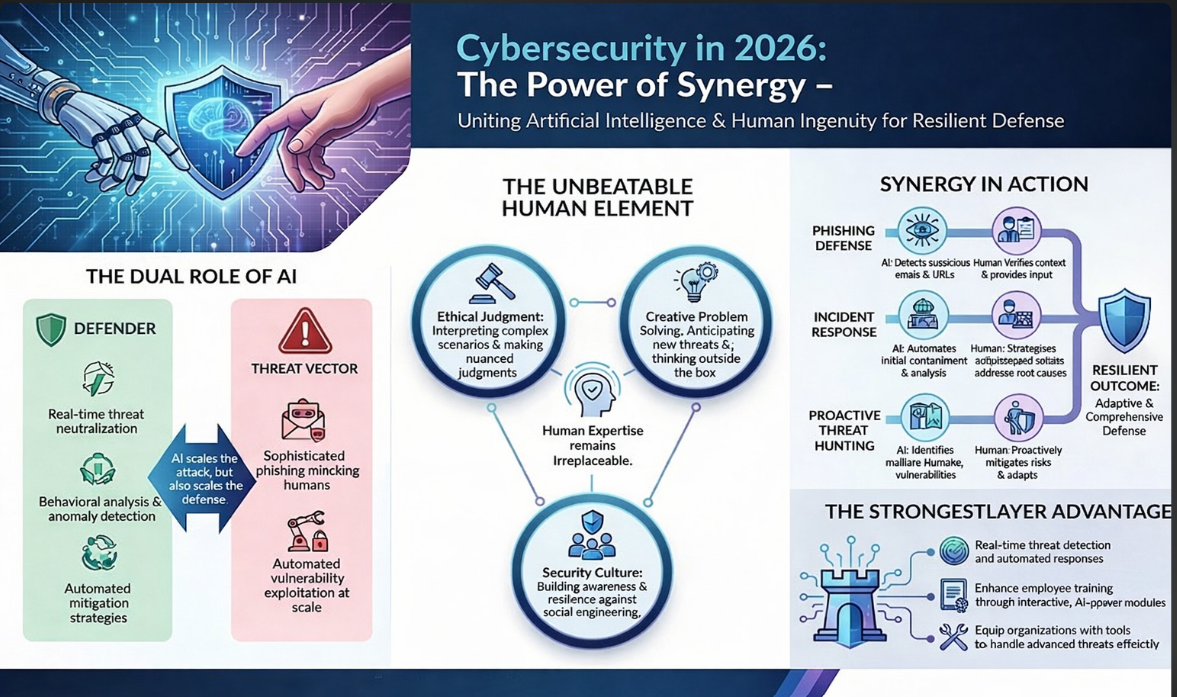
Cyber threats in 2026 have escalated with AI-powered attacks like adversarial machine learning and automated ransomware variants, demanding defenses that operate at machine speed. This stark reality, highlighted by leading security research, signals the end for isolated, siloed security tools. In this new era, the battle is no longer human versus machine, but machine versus machine. To survive, organizations need integrated solutions that deliver real-time protection and autonomous response. This is where AI cybersecurity platforms emerge as the non-negotiable foundation of modern defense. For a broader understanding of the evolving threat landscape, see our analysis of Explosive Cybersecurity Threats: Key Trends, Predictions, and Defense Strategies for 2025.

This guide defines AI cybersecurity platforms as the integrated solutions that unify detection, response, and posture management with AI-native layers for automated threat detection and ransomware AI defense within Zero Trust AI frameworks. We will explore their core mechanics, their indispensable role in operationalizing Zero Trust, and the strategic roadmap they provide toward Security AI 2026.
The Escalating Threat Landscape: Why Old Defenses Fail
The digital battlefield is evolving at a breakneck pace. Adversaries are no longer just script kiddies; they are leveraging artificial intelligence to create attacks that learn, adapt, and propagate with terrifying efficiency. Research indicates we are facing:
- Adversarial Machine Learning: Attacks designed to fool AI models by injecting malicious data or manipulating inputs, compromising the very tools meant to protect us.
- Automated Ransomware Variants: Self-propagating malware that can identify high-value targets, encrypt data, and negotiate ransoms without human intervention.
- AI-Powered Social Engineering: Hyper-personalized phishing campaigns generated at scale, making them nearly indistinguishable from legitimate communication.

Traditional, signature-based defenses and point solutions are utterly overwhelmed. They operate on known threats, leaving a vast blind spot for novel, zero-day attacks. The new paradigm requires defenses that operate at machine speed—capable of analyzing billions of events in real-time, identifying subtle anomalies, and responding autonomously before human analysts are even aware of the breach. This is the fundamental problem that AI cybersecurity platforms are built to solve, moving beyond isolated tools to deliver a cohesive, intelligent shield.
What Is an AI Cybersecurity Platform?
An AI cybersecurity platform is not merely a tool with an AI feature bolted on. It is a consolidated, unified system that integrates traditionally siloed capabilities—such as application security testing (AST), software supply chain security (SSCS), endpoint protection, and Security Information and Event Management (SIEM)—under a single, AI-native intelligence layer. This architecture enables real-time correlation and analysis across the entire IT estate, from code to cloud.
Think of it as a central nervous system for your security posture. Instead of having separate “brains” for network monitoring, endpoint protection, and code scanning, a unified AI cybersecurity platform provides one intelligent core that sees and understands everything in context.
Real-World Examples:
- Cycode integrates AST, Application Security Posture Management (ASPM), and SSCS with powerful AI features. Its Exploitability Agent uses AI to achieve a 94% reduction in false positives, while its Context Intelligence Graph provides complete code-to-cloud traceability, showing how a vulnerability in a developer’s code could impact a production workload.
- Platforms like CrowdStrike Falcon and SentinelOne Singularity provide endpoint and cloud protection powered by behavioral AI. This AI doesn’t rely on known malware signatures. Instead, it continuously scans network traffic, endpoint processes, and user behaviors, building a baseline of “normal” and flagging any deviation that could indicate a threat—whether it’s a zero-day exploit or an insider risk.
The power of these AI cybersecurity platforms lies in this unification. A suspicious process on an endpoint can be instantly correlated with anomalous network traffic and a recent, vulnerable code deployment, allowing the platform to understand the full attack chain in seconds, not days.
The Core Engine: Automated Threat Detection
At the heart of every AI cybersecurity platform is its capability for automated threat detection. This is where AI and machine learning models ingest massive streams of telemetry—logs, network flows, process executions, cloud API calls—and analyze them in real-time for anomalies that signal malicious activity.

This process moves far beyond simple alerting. Modern platforms use agentic AI—AI agents designed to perform specific security tasks autonomously. For example, platforms like Checkmarx One and Microsoft Sentinel employ such agents to provide end-to-end coverage across applications, containers, and cloud environments. These agents don’t just find problems; they prioritize them based on severity, exploitability, and business context, dramatically cutting through the noise that causes analyst fatigue.
Consider how SentinelOne’s behavioral AI works: It establishes a baseline for every device and user. If a process suddenly begins encrypting files (a hallmark of ransomware) or attempts lateral movement across the network, the AI immediately recognizes this as a severe deviation. Crucially, it doesn’t just alert; it can trigger an autonomous response, such as:
- Quarantining the affected endpoint from the network.
- Killing the malicious process.
- Rolling back encrypted files to a safe, pre-attack state.
The benefits are transformative: Speed (response in milliseconds), Accuracy (drastically reduced false positives), and Scalability (protecting millions of events without adding staff). This makes automated threat detection the indispensable engine of a modern AI cybersecurity platform.
A Critical Application: Ransomware AI Defense
Ransomware remains a top existential threat, but its nature has changed. Modern ransomware is often “fileless,” residing in memory, or uses living-off-the-land techniques (LOLBins) that leverage legitimate system tools. This evades traditional antivirus software completely. This is where specialized ransomware AI defense within a platform shines.

These defenses use layered machine learning models, sandboxing, and threat intelligence graphs to identify early attack indicators long before the encryption starts. They look for behavioral anomalies like:
- Mass file reads or unusual process chains.
- Attempts to disable security software or backup services.
- Command-and-control (C2) communication patterns.
Leading AI cybersecurity platforms have built powerful, specific countermeasures. SentinelOne Singularity offers one-click remediation and its “Purple AI” for automating threat investigations. CrowdStrike excels at mapping the entire attack chain—from initial access to data exfiltration—allowing for precise containment that halts ransomware before it can spread laterally.
This represents a shift from reactive recovery to proactive defense. The platform’s automated threat detection identifies the precursor behaviors, and its ransomware AI defense modules execute a pre-programmed playbook to isolate and neutralize the threat, often without requiring a human decision. This seamless integration is the hallmark of a true platform approach.
The Strategic Framework: Zero Trust AI
The Zero Trust security model—”never trust, always verify”—has become a strategic imperative. However, implementing it manually is impossible at scale. How do you continuously verify every user, device, and data flow in a dynamic cloud environment? The answer is Zero Trust AI.

Zero Trust AI is the embodiment of this principle through continuous, AI-enforced checks. AI cybersecurity platforms are the engines that make Zero Trust operational by providing:
- Dynamic Authentication & Access Control: Using AI to analyze context (user behavior, device health, location) to adjust access privileges in real-time, rather than relying on static permissions.
- Anomaly Detection in Behaviors: Continuously verifying that authenticated users are acting normally. Is a finance employee suddenly trying to access source code repositories? The AI flags it.
- Policy Enforcement at Scale: Automatically applying and enforcing least-privilege policies across hybrid environments, something no human team could manage manually.
Platforms like CrowdStrike unify telemetry into an enterprise graph, making all data AI-ready for this continuous verification. SentinelOne extends governance across development pipelines, detecting adversarial inputs like prompt injection attacks against AI models. Furthermore, solutions like Cycode’s AI Guardrails extend Zero Trust principles to the AI model development lifecycle and software supply chain, ensuring that the AI tools you use are themselves secure and compliant.
In essence, AI cybersecurity platforms don’t just protect your assets; they actively and intelligently manage the trust relationships between them, creating an adaptive, resilient security posture that moves as fast as your business.