The AI Cybersecurity Platform Revolution: Your 2026 Guide to Automated Defense
Estimated reading time: 8 minutes
Key Takeaways
- Modern ai cybersecurity platforms are unified systems that integrate machine learning, behavioral analytics, and AI-native tools to deliver proactive, automated defense across your entire digital estate.
- These platforms shift security from a reactive, signature-based model to a predictive one, capable of reducing false positives by up to 94% through advanced AI agents and context intelligence.
- Core capabilities you must understand include automated threat detection, specialized ransomware AI defense, and the integration of zero trust ai principles.
- The landscape of security ai 2026 is defined by predictive AI, autonomous response playbooks, and an escalating AI arms race between attackers and defenders.
- Successful implementation requires careful evaluation of integration capabilities, AI governance, and maintaining skilled human oversight to guide the technology.
Table of contents
- The AI Cybersecurity Platform Revolution: Your 2026 Guide to Automated Defense
- Key Takeaways
- The Urgency of AI-Driven Security
- Automated Threat Detection: The Engine of Modern Defense
- Ransomware AI Defense: Stopping the Digital Kidnapper
- Zero Trust AI: Continuous Verification in an Untrusted World
- Security AI 2026: Trends Shaping the Future
- Implementing AI Cybersecurity Platforms: A Practical Guide
- Frequently Asked Questions
With cyber threats evolving at a breakneck pace, a staggering volume of attacks now bypass traditional defenses, making the shift to intelligent, autonomous systems not just an advantage but a necessity. This is where ai cybersecurity platforms enter the stage—unified systems that integrate machine learning, behavioral analytics, and AI-native tools to deliver automated, proactive defense across applications, endpoints, cloud environments, and supply chains. This stands in stark contrast to the reactive, signature-based security and manual triage of the past, emphasizing a critical shift to real-time threat prediction and autonomous response. Research indicates these platforms can reduce false positives by up to 94% through advanced AI exploitability agents and context intelligence graphs, fundamentally changing the security game.

This guide is your essential roadmap for 2026. We will dissect the core components that make these platforms transformative, covering the mechanics of automated threat detection, the specialized power of ransomware AI defense, the seamless integration of zero trust ai principles, and the forward-looking innovations defining security ai 2026. By understanding these elements, you can navigate the complex landscape of AI-driven threat detection and defense with confidence.
Automated Threat Detection: The Engine of Modern Defense
At the heart of every advanced ai cybersecurity platforms lies its engine: automated threat detection. This is the capability that moves security teams from constantly chasing alerts to proactively managing risk. It works by employing sophisticated machine learning models to perform behavioral analysis, signature-less detection, and real-time correlation of events streaming from endpoints, application logs, and network traffic.
Instead of looking for known malicious code, these systems learn the normal “pattern of life” for every user, device, and application. When deviations occur—like a user accessing sensitive data at an unusual hour or an application making unexpected network calls—the AI flags it instantly. This approach is critical for catching zero-day exploits and sophisticated, stealthy attacks that traditional tools miss.
Leading platforms exemplify this power in action:
- CrowdStrike Falcon leverages what it calls “enterprise-scale telemetry graphs” and mission-ready AI agents. This allows for dynamic data modeling and natural language-driven investigations, enabling analysts to ask complex questions about their security posture and get immediate, actionable answers.
- SentinelOne Singularity employs behavioral AI designed specifically to hunt zero-day threats. Its crowning feature is a one-click rollback capability, allowing security teams to not just detect but instantly revert malicious actions, restoring systems to a pre-attack state.
- For holistic visibility, platforms like Elastic Security and Hunters AI-Driven SIEM provide scalable analytics tailored for hybrid cloud environments. They automate entire security workflows, from ingestion to correlation and response, drastically minimizing the need for manual intervention and accelerating mean time to respond (MTTR).
This evolution in automated threat detection transforms security operations centers (SOCs) from reactive war rooms into intelligent, predictive nerve centers.
Ransomware AI Defense: Stopping the Digital Kidnapper
Ransomware remains a top-tier threat, crippling businesses with encryption and extortion. Modern ai cybersecurity platforms have risen to the challenge with specialized ransomware AI defense capabilities. These go beyond simple malware detection to understand the entire attack chain of a ransomware operation.

These defenses work by layering AI techniques:
- Behavioral Monitoring: Detecting the tell-tale signs of ransomware, such as rapid, sequential file encryption, anomalous file access patterns, and communication with known command-and-control servers.
- Attack Chain Mapping: Using AI to correlate seemingly unrelated events across the network to piece together the full narrative of an attack, from initial phishing email to lateral movement and data exfiltration.
- Sandboxing & Static Analysis: Detonating suspicious files in isolated environments to observe their behavior without risk to production systems.
Key players in this space demonstrate the life-saving potential of AI:
- SentinelOne Singularity shines here with real-time ransomware detection that triggers automated remediation. Its patented rollback technology is a game-changer, allowing organizations to restore encrypted files and systems instantly, negating the attacker’s leverage.
- Bitdefender GravityZone offers robust protection against fileless attacks (which reside only in memory) and provides advanced forensics visualization. This helps teams understand the scope of an attack quickly and ensure complete eradication.
- On the vulnerability front, Cycode’s AI Exploitability Agent introduces a critical triage function. It doesn’t just find vulnerabilities; it uses AI to autonomously determine which ones are actually exploitable in a production environment, allowing teams to focus on the risks that truly matter and prevent ransomware actors from leveraging known flaws.
This focused ransomware AI defense turns a potentially business-ending event into a managed incident.
Zero Trust AI: Continuous Verification in an Untrusted World
The Zero Trust model—”never trust, always verify”—is a perfect philosophical partner for AI. Implementing it manually at scale is nearly impossible, but ai cybersecurity platforms make it operational through zero trust ai. Here, AI acts as the continuous, intelligent verifier, analyzing every access request in real-time against a contextual understanding of risk.

Zero trust ai within a platform means:
- Dynamic Policy Enforcement: AI analyzes the context of an access request (who, what, when, where, device health) to enforce least-privilege policies dynamically, rather than relying on static rules.
- Unified Telemetry Analysis: By correlating identity, endpoint, network, and workload data, the AI builds a holistic risk score for every transaction, enabling more accurate allow/deny decisions.
- Anomalous Behavior Detection: Even with valid credentials, AI can flag and block behavior that deviates from a user’s or service’s normal pattern, a key tenet of Zero Trust.
Platforms are building this intelligence directly into their fabric:
- CrowdStrike Falcon positions itself as an agentic platform supporting Zero Trust, deploying AI agents across data, models, and infrastructure to make continuous, micro-level security decisions.
- Checkmarx One excels in correlating signals from code to cloud. This allows for role-based enforcement in development and deployment pipelines, ensuring that access to critical code repositories and cloud environments is tightly governed by AI-driven policy.
- GitHub Advanced Security integrates AI-powered remediation suggestions directly into developer workflows. This embeds zero trust ai principles at the code level, fixing security issues before they are ever deployed, which is the most cost-effective and low-friction form of enforcement.
Through zero trust ai, platforms ensure that security is adaptive, contextual, and woven into the fabric of every digital interaction.
Security AI 2026: Trends Shaping the Future
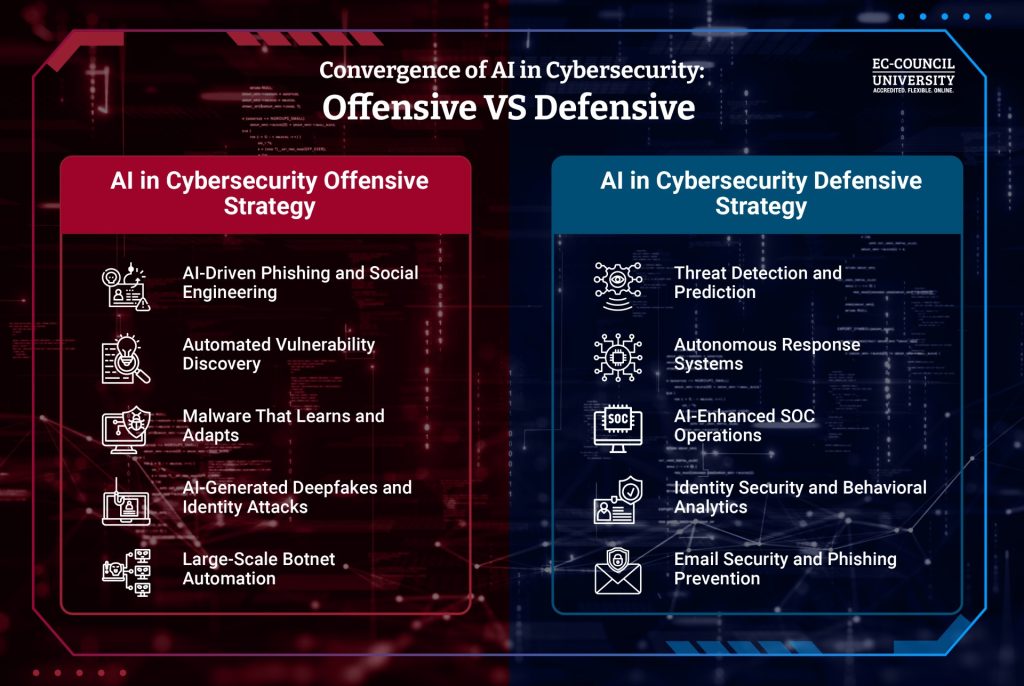
The trajectory of security ai 2026 points toward a more predictive, autonomous, and deeply integrated future for ai cybersecurity platforms. We are moving from AI that detects to AI that predicts and acts. This evolution is fueled by an escalating arms race, where attackers also leverage AI, making defender innovation non-optional.

Key trends to watch include:
- Predictive AI and Autonomous Response: Platforms will increasingly move from “what happened” to “what will happen.” Using predictive analytics, they will identify precursor signals to an attack and execute automated response playbooks without human intervention, containing threats in milliseconds.
- The Rise of Agentic AI: Think of AI “agents” as autonomous workers with specific goals. Tools like Charlotte AI AgentWorks enable no-code orchestration of these agents for complex security tasks. Furthermore, coverage for emerging threats like those in the OWASP LLM Top 10 (specific to Large Language Model security) will become standard.
- Unified ASPM (Application Security Posture Management): The silos between application security and cloud security are dissolving. Future platforms will offer complete code-to-cloud traceability, giving a single pane of glass for risk across the entire software development lifecycle and runtime environment.
- Enhanced Core Controls: As AI becomes more pervasive, the foundational controls around it must strengthen. This includes deep visibility into all AI model usage, strong authentication for AI system access, and continuous monitoring. Platforms like FortiAI are already working to enhance threat intelligence sharing across firewalls, endpoints, and other security fabrics.

The landscape of security ai 2026 is one where ai cybersecurity platforms become the central, intelligent brain of an organization’s defense, capable of autonomous action based on a predictive understanding of risk.
Implementing AI Cybersecurity Platforms: A Practical Guide
Adopting a powerful ai cybersecurity platforms requires more than just a purchase order; it demands strategic planning. Here’s how to approach implementation for maximum impact and minimal disruption.

Evaluation Criteria: When assessing platforms, look beyond marketing claims. Key metrics include:
- False Positive Reduction: A core promise of AI is cutting through alert noise. Demand data on their platform’s efficacy in reducing false alerts.