Here is the enhanced blog post with 8 visually relevant images inserted at optimal points to break up the text, support key concepts, and improve reader engagement.
The Critical Zero-Day Vulnerability Cloud Platforms 2025 – Immediate Response Guide for AWS, Azure, and Google Cloud
Estimated reading time: 7 minutes
Key Takeaways
- A critical zero-day vulnerability cloud platforms 2025 have discovered is now actively exploited across AWS, Azure, and Google Cloud.
- The vulnerability allows for unauthenticated remote code execution with a CVSS score of 9.8 to 10.0.
- Enterprise cloud vulnerability data breach risk is extremely high, with potential for lateral movement and data exfiltration.
- A cloud security patch emergency update is required immediately to mitigate the threat.
- Security teams must implement behavior-based detection and pre-defined incident response playbooks to mitigate zero-day cloud exploit effectively.
Table of contents
- The Critical Zero-Day Vulnerability Cloud Platforms 2025 – Immediate Response Guide for AWS, Azure, and Google Cloud
- Key Takeaways
- Introduction and Severity Overview
- The 2025 Zero-Day Landscape – Why This Is Different
- Symantec’s Advisory and Official Responses
- The Immediate Threat – Enterprise Cloud Vulnerability and Data Breach Risk
- The Emergency Patch – Cloud Security Patch Emergency Update
- Mitigation Guide – How to Mitigate Zero-Day Cloud Exploit
- Conclusion and Final Recommendations
- Frequently Asked Questions
Introduction and Severity Overview
A critical zero-day vulnerability cloud platforms 2025 have discovered is now threatening enterprise infrastructure across AWS, Azure, and Google Cloud. Security teams are on high alert as active exploitation has been confirmed. This particular vulnerability allows for unauthenticated remote code execution (RCE) at a CVSS score of 9.8 to 10.0, similar to the React2Shell (CVE-2025-55182) and Oracle EBS (CVE-2025-61882) cases from recent research. The enterprise cloud vulnerability data breach risk is immediate and severe.

The 2025 Zero-Day Landscape – Why This Is Different
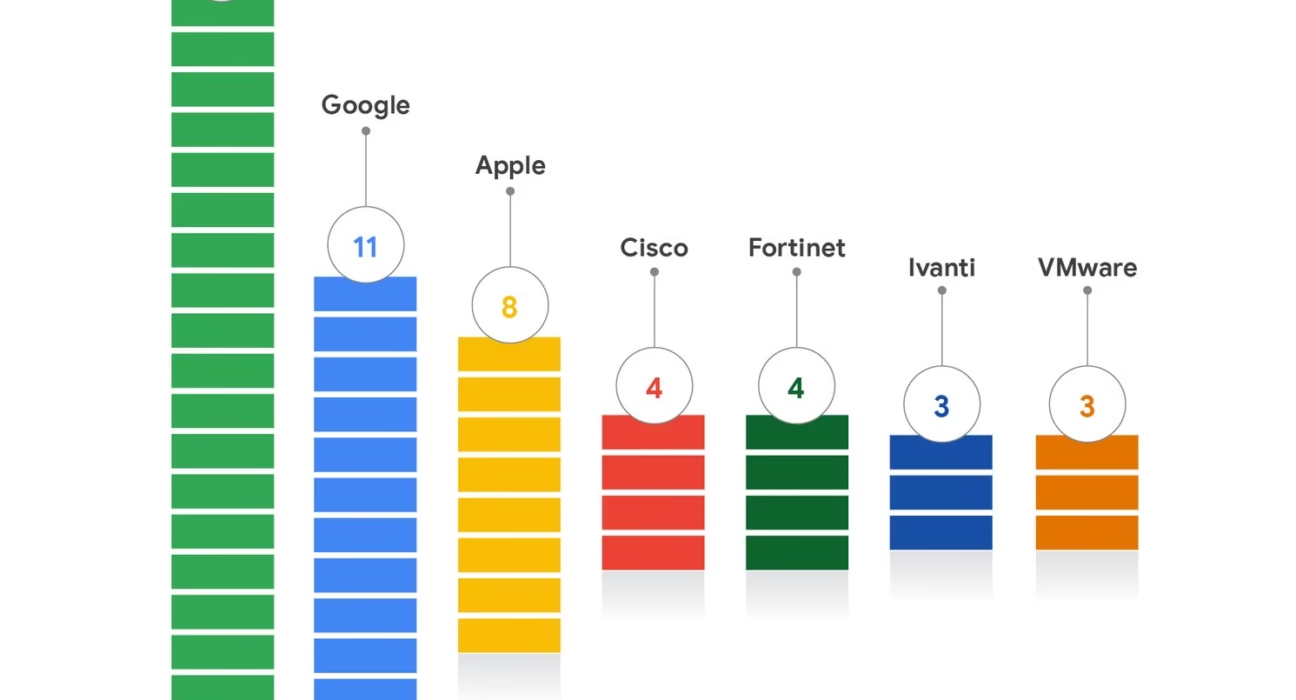
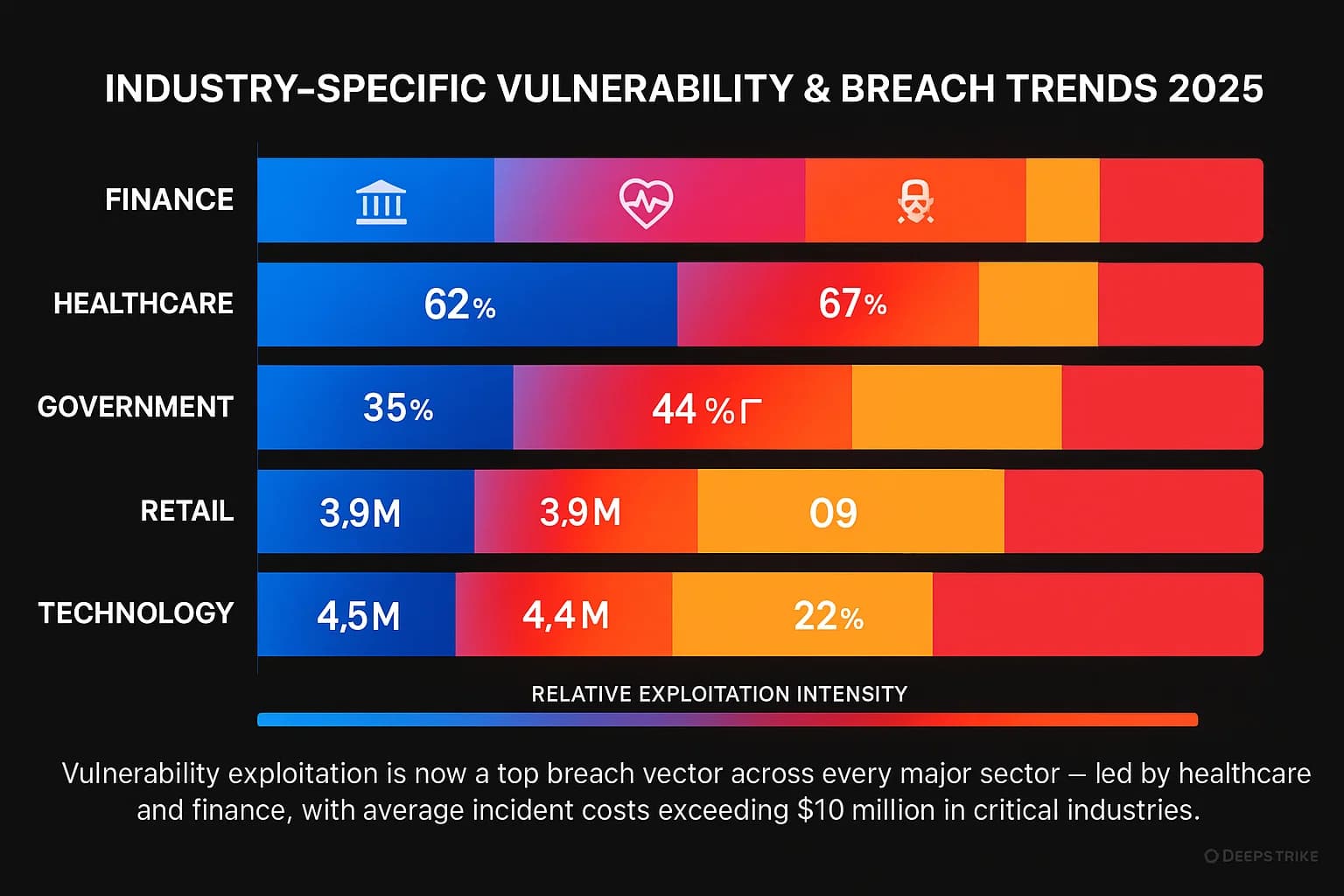
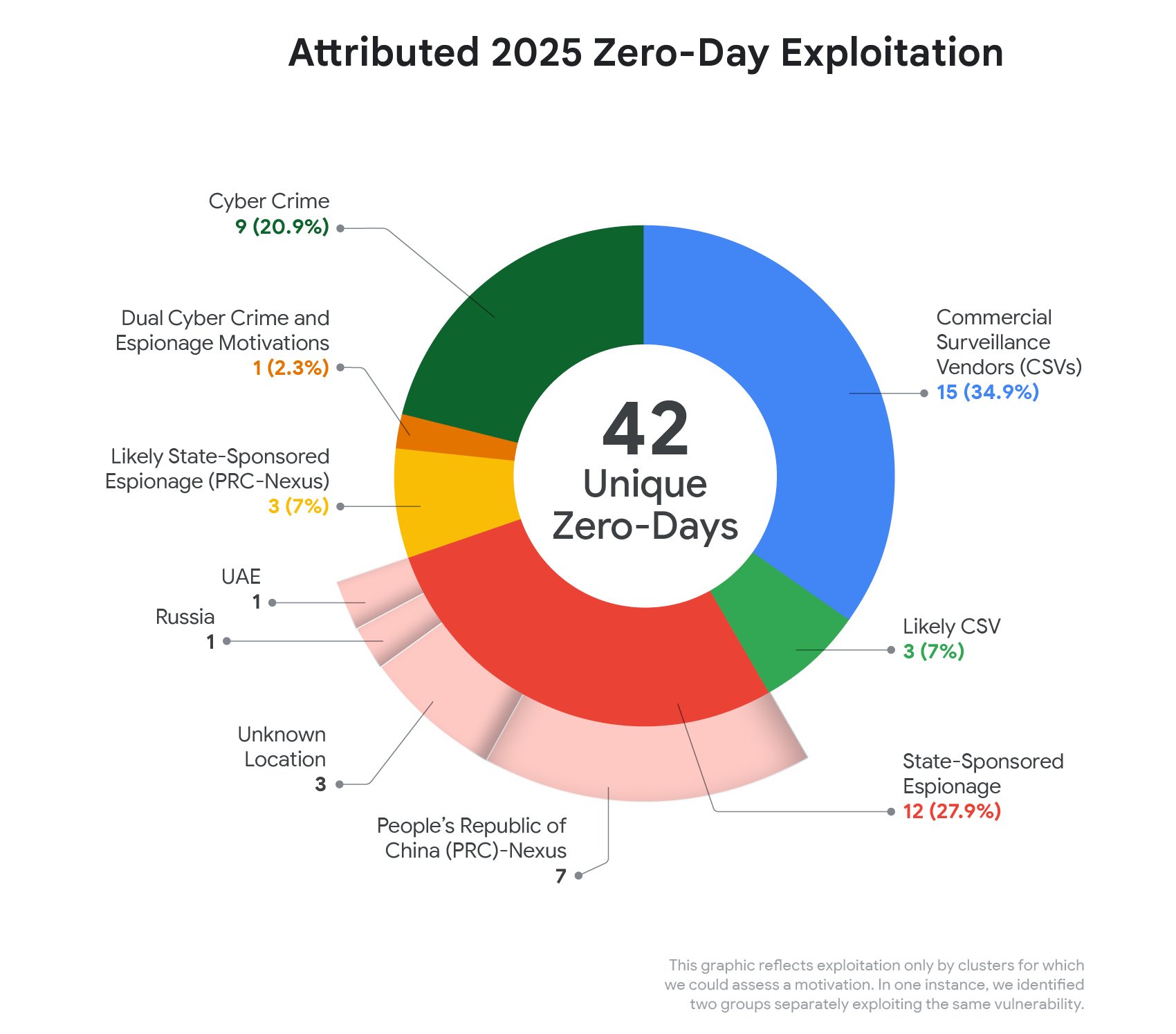
Google’s Threat Intelligence Group has reported: “We tracked 90 exploited zero-day vulnerabilities in 2025, up from 78 in 2024. Notably, 48% targeted enterprise technologies – an all-time high.” This critical zero-day vulnerability cloud platforms 2025 is not an isolated incident but part of a surge in enterprise-focused zero-days, with security and networking appliances accounting for half (21) of those enterprise exploits. For more on these broader cybersecurity trends and threats, read our guide on the explosive cybersecurity threats for 2025. Since cloud platforms host enterprise workloads, this vulnerability is a direct attack vector against the foundational layer of modern IT, increasing the enterprise cloud vulnerability data breach risk dramatically.

Symantec’s Advisory and Official Responses
A Symantec zero-day advisory aws azure google cloud has been issued, warning that attackers are actively scanning for vulnerable instances across all three major providers. While Symantec and other threat intel vendors have not named a single specific CVE affecting all three simultaneously, the patterns of exploitation impact the infrastructure that underpins these clouds. The breakdown by platform is as follows:
- AWS: Vulnerable EC2 instances running outdated application servers (e.g., React Server Components from React2Shell).
- Azure: Virtual machines and Azure App Services running vulnerable Oracle EBS or Citrix deployments.
- Google Cloud: Compute Engine instances where security appliances (e.g., CitrixBleed 2) are unpatched.
CitrixBleed 2 (CVE-2025-5777) was disclosed and patched June 17, 2025, with exploitation observed immediately post-disclosure. Check the official advisory for more details: Citrix advisory for CVE-2025-5777. The Symantec zero-day advisory aws azure google cloud emphasizes that immediate action is needed.

The Immediate Threat – Enterprise Cloud Vulnerability and Data Breach Risk
The enterprise cloud vulnerability data breach risk is extremely high. An unpatched instance can lead to lateral movement, data exfiltration, and ransomware deployment. The attack progression follows a realistic scenario: the attacker exploits the zero-day on a publicly-facing cloud server, gains an initial foothold with SYSTEM/root privileges, moves laterally to databases and storage services, and exfiltrates sensitive data or deploys ransomware. The CL0P group’s campaign against Oracle EBS (CVE-2025-61882) was exploited from August 9, 2025, until the patch on October 4, 2025 – a 2-month exposure window. Financial actors like CL0P now drive a growing share of zero-day exploitation. For the official advisory, see CISA advisory on CVE-2025-61882.
The Emergency Patch – Cloud Security Patch Emergency Update
A cloud security patch emergency update is required immediately. Patches are available from your cloud provider and affected software vendors. Apply within 24 hours. Research shows that organizations that delay patching remain exposed for weeks or months (as seen with the Oracle EBS case). Specify patch locations:
- AWS Security Bulletins: AWS Security Bulletins
- Azure Health: Azure Service Health
- Google Cloud Security Advisories: GCP Security Advisories
A key insight from the research is that patches don’t remove risk overnight. Organizations face significant testing and operational constraints that leave them exposed for weeks or months after fixes are released. For a deeper analysis, see this report from SANS on patch deployment delays. The cloud security patch emergency update must be prioritized and automated where possible.
.jpg)
Mitigation Guide – How to Mitigate Zero-Day Cloud Exploit
Here is exactly how to mitigate zero-day cloud exploit across your enterprise. Follow these five steps:
Step 1: Inventory vulnerable resources. Use cloud asset management tools (e.g., AWS Config, Azure Policy, GCP Asset Inventory) to identify all instances running affected software (React Server Components, Oracle EBS, Citrix appliances). Scan for any unapproved or “shadow IT” instances.

Step 2: Apply the emergency patch. Deploy the patch from the cloud provider’s security advisory. Use automation (e.g., AWS Systems Manager Patch Manager, Azure Update Management) to expedite.
Step 3: Implement compensating controls while patching. If you cannot patch immediately, deploy Web Application Firewall (WAF) rules to block known exploit signatures, enforce strict network segmentation to limit lateral movement, and lock down IAM policies to prevent privilege escalation. For more on leveraging cutting-edge AI for advanced security, check out this guide on breakthrough AI cyber defense.
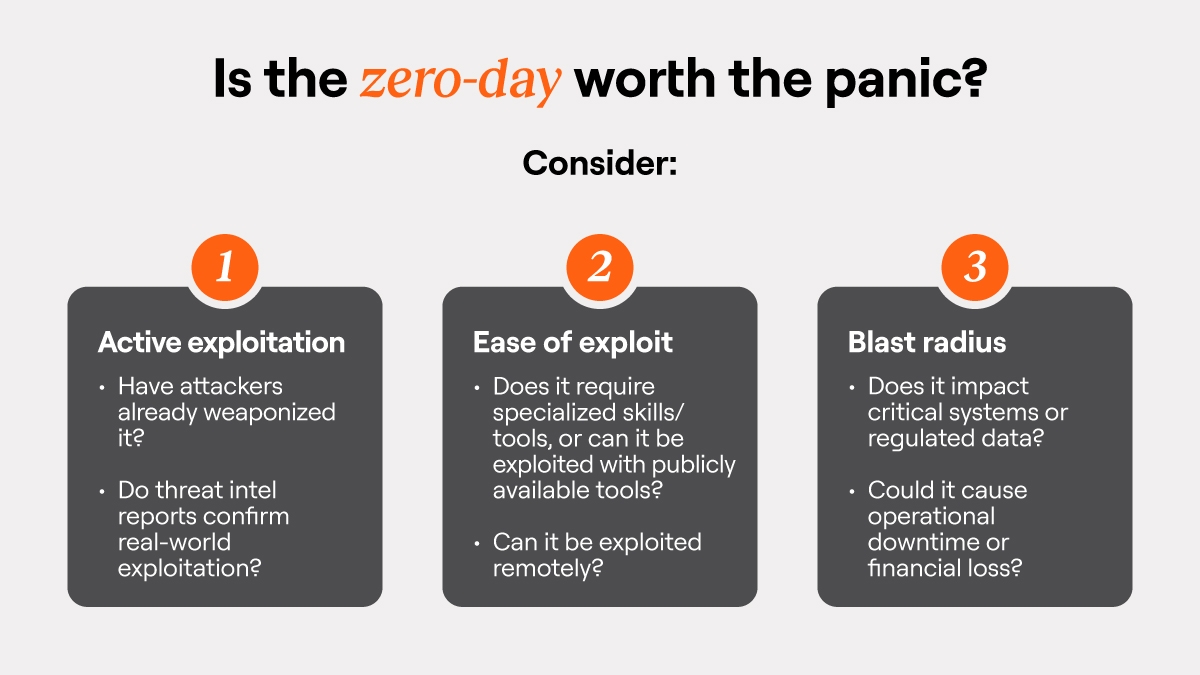
Step 4: Scan for indicators of compromise (IOCs). Even before patching, run IOC scans using threat intelligence feeds from Symantec, CrowdStrike, or your SIEM. Look for unusual outbound traffic, new admin accounts, or unexpected process executions.
Step 5: Establish pre-defined incident response playbooks. Behavior-based detection is more effective than waiting for patches. Create playbooks with clear triggers for future zero-days. For guidance, see this CrowdStrike guide on behavior-based detection. Following these steps will help you effectively mitigate zero-day cloud exploit.

Conclusion and Final Recommendations
The critical zero-day vulnerability cloud platforms 2025 underscores the ongoing risk to enterprise cloud environments. The 2025 zero-day landscape shows no signs of slowing down – 90 zero-days already this year, with enterprise targets at an all-time high. Rapid response is not optional; it is essential for survival. To understand how to secure your personal devices against these threats, also read our complete guide on how to secure your smartphone in 2025. Take the following actions now:
- Subscribe to Symantec and cloud provider security advisories.
- Implement automated patch management cycles.
- Invest in behavior-based threat detection tools.
- Conduct a zero-day response drill with your incident response team.
The critical zero-day vulnerability cloud platforms 2025 is a stark reminder that proactive defense and immediate patching are non-negotiable in today’s threat landscape.
Frequently Asked Questions
-
What is the critical zero-day vulnerability cloud platforms 2025?
It is a severe vulnerability allowing unauthenticated remote code execution on AWS, Azure, and Google Cloud, with a CVSS score of 9.8 to 10.0.
-
Which platforms are affected by this vulnerability?
All three major cloud platforms – AWS, Azure, and Google Cloud – are impacted, particularly instances running vulnerable software like React Server Components, Oracle EBS, or Citrix appliances.
-
What is the enterprise cloud vulnerability data breach risk?
The risk is extremely high as attackers can move laterally, exfiltrate data, and deploy ransomware from a single unpatched instance.
-
How can I mitigate zero-day cloud exploit in my environment?
Follow the five-step mitigation guide: inventory resources, apply emergency patches, implement WAF rules, scan for IOCs, and establish incident response playbooks.
-
Where can I find the cloud security patch emergency update?
Patches are available via AWS Security Bulletins, Azure Service Health, and Google Cloud Security Advisories. Links are provided in Section 4 of this article.